Share Article
Purchasing an EV Code Signing Certificate for Azure
Azure Key Vault is a service provided by Microsoft which can be used to manage keys, secrets, and certificates. These are all stored in hardware security modules (HSMs) that comply with industry standards such as the Federal Information Processing Standards (FIPS) 140-2 Level 2.

Using Azure Key Vault
Azure Key Vault is a service provided by Microsoft which can be used to manage keys, secrets, and certificates. These are all stored in hardware security modules (HSMs) that comply with industry standards such as the Federal Information Processing Standards (FIPS) 140-2 Level 2. This means that Extended Validation (EV) Code Signing certificates can be issued to an Azure Key Vault removing the requirement for issuance to a cryptographic token.
You can use the instructions on this page to set up, install, and use an EV Code Signing certificate in Azure.
- Order a EV Codesign certificate through the TRUSTZONE portal, if the product is not showing up in the product list please contact your TRUSTZONE account manager to get the product activated in your portal.
- During the ordering process you will asked to create a pickup password. Please store this password in a safe location as this password cannot be reset and would require the order to be cancelled and reordered if forgotten.
- When the order has been placed the vetting process will start. To complete the vetting process you will need to sign EV documentation, sent by the Vetting Team and confirm the order through an approved company number.
- To set up the Azure Key Vault please log in to your Azure Portal and click on the “Create a resource” button. Search for “Key Vault” and press create to get your vault up and running
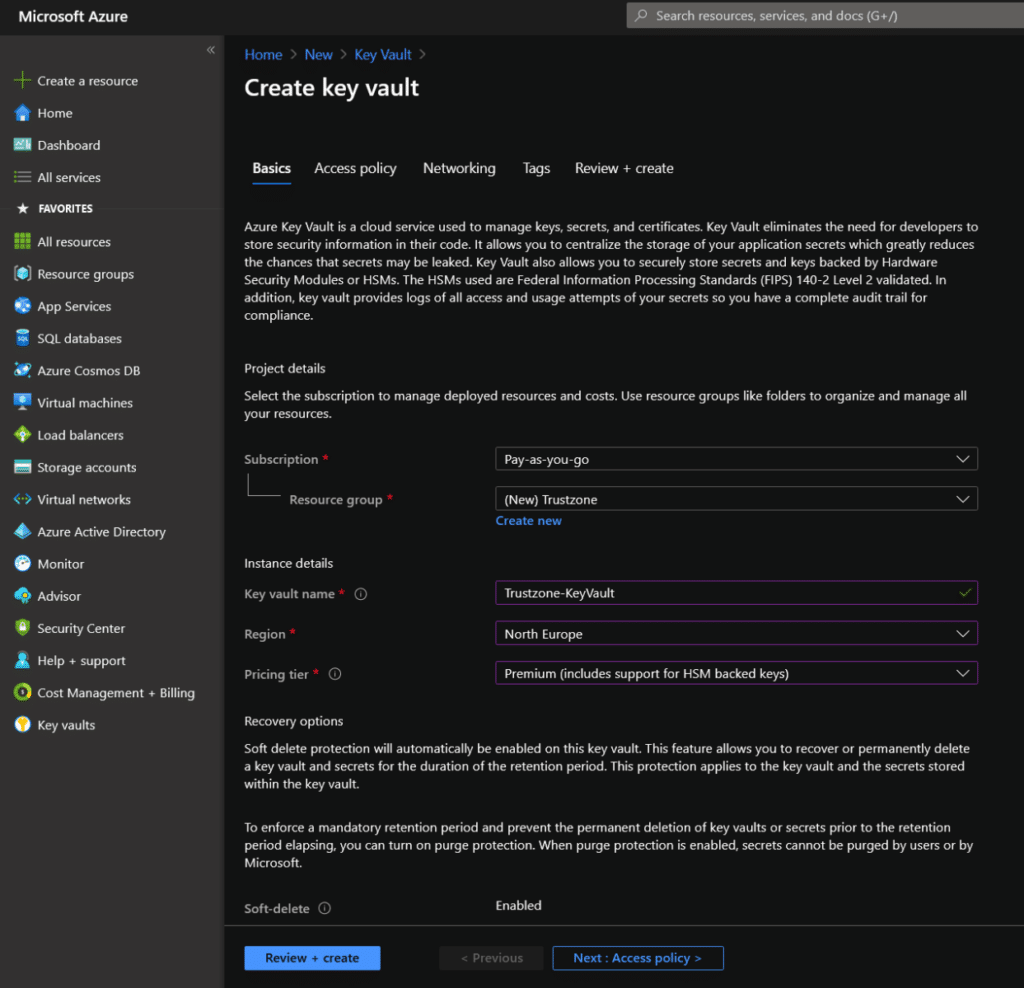
- Please select the settings that fit your use case and create your Key Vault.
Note: In order to be compliant with the FIPS 140-2 standard, you should select the “Premium” pricing tier. If you do not choose “Premium”, there’s a risk that your certificate will be revoked.
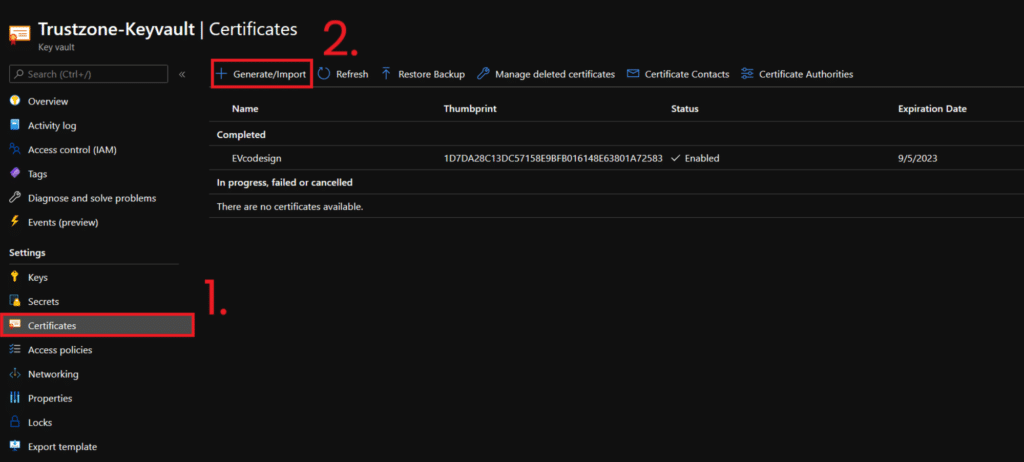
- When your vault has been created, please select “Certificates” in the action bar to the left.
- Then click “Generate/Import” to start creating your Code Signing CSR:
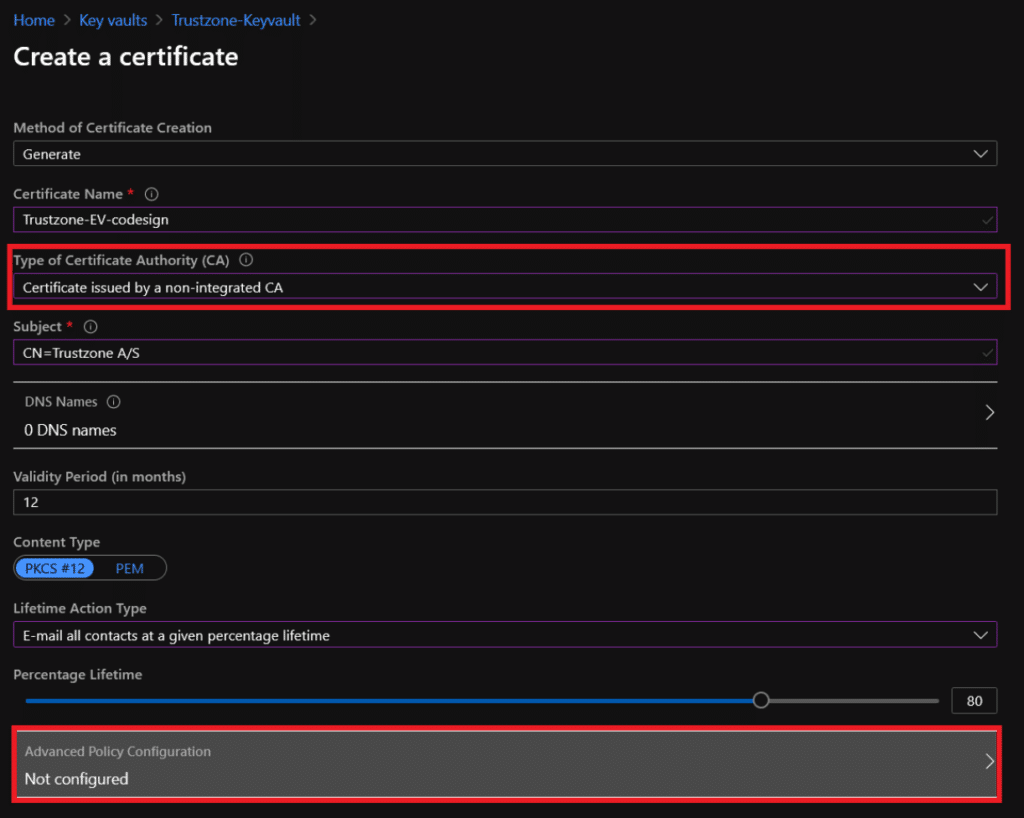
- Fill out your certificate name and subject name. The subject name should be your company name.
- Set the Type of Certificate Authority to non-integrated CA and then select Advanced Policy Configuration:
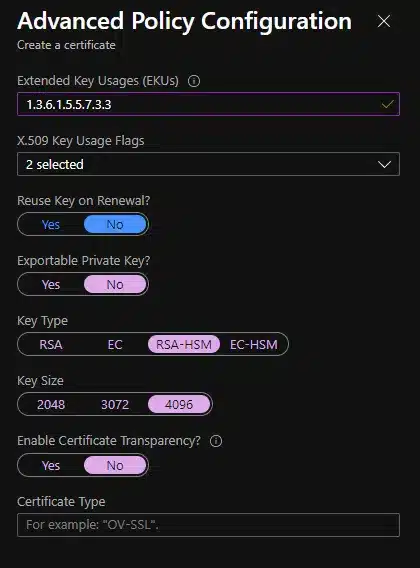
- In the Extended Key Usages (EKUs) field please add the following: 1.3.6.1.5.5.7.3.3. This EKU identifies the certificate as a Code Signing certificate. You should also set “Exportable Private Key” as No and the “Key Type” to RSA-HSM.
Note: Since May 2021, all Code Signing certificates from TRUSTZONE are required to be issued with 4096-bit keys.
- When you have configured the policy, click “Okay” and then “Create”. The certificate will then appear as an “In progress” certificate under the Certificates tab:
- Click on your certificate in progress. Choose “Certificate Operation” and then click “Download CSR”:
The generation process
Now you’re ready to generate your EV Code Signing (HSM). When the vetting process is completed you will receive an email letting you know that your certificate is ready for pickup.
When you receive this email, simply click the pickup link and go through the steps, inputting your pickup password when prompted and copy-pasting the contents of your CSR file when asked. You will then be prompted to download your certificate. Save the certificate in the location of your choosing.
- Now, log in to your Azure Portal again and go to your Key Vault. Click on your certificate in progress. Choose “Certificate Operation” and then click “Merge Signed Request”. Find your downloaded certificate and upload it to the Key Vault:
Your EV Code Signing certificate is now available in Azure Key Vault and can be used in Azure Pipeline or with the Azure Sign Tool.

